This course will familiarize students with all aspects of Linux forensics. By the end of this course students will be able to perform live analysis, capture volatile data, make images of media, analyze filesystems, analyze network traffic, analyze files, perform memory analysis, and analyze malware all on a Linux system with readily available free and open source tools. Students will also gain an in-depth understanding of how Linux works under the covers.
A non-exhaustive list of topics to be covered includes:
- Live response
- First talk to the humans
- What do they think happened
- Details on victim system(s)
- Mount response kit with known good tools
- cdrom preferred as it was not likely part of compromise
- USB MS can be used if no CDROM
- Using netcat to minimize contamination
- Collecting volatile data
- date and time
- network interfaces
- funny networks
- promiscuous mode?
- network connections
- open ports
- programs associated with ports
- running processes
- open files
- routing tables
- mounted filesystems
- loaded kernel modules
- Collecting data to determine if dead analysis is justified
- kernel version
- uptime
- filesystem datetime stamps
- hash values for system files
- current user logins
- login history
- system logs
- user accounts
- user history files
- hidden files and directories
- sending off suspicious files for further study
- Dumping RAM
- Making the decision to dump RAM
- Using fmem
- Using LiME
- Using /proc/kcore
- First talk to the humans
- Acquiring filesystem images
- Using dd
- Using dcfldd
- Write blocking options
- Forensic Linux distros
- Udev rules based blocker
- Analyzing filesystem images
- Mounting images
- Files with basic system info
- Files with suspicious user info
- Examining logs
- Process-related files
- Authentication-related files
- Using standard Linux tools to find information
- Strange files
- Regular files in /dev
- User history files
- Hidden files
- SUID/SGID files
- Detecting backdated files
- Recovering deleted files
- Finding deleted files
- Attempting recovery
- Leveraging The Sleuth Kit (TSK) and Autopsy
- mmls
- fsstat
- dstat
- istat
- fls & mactime
- Mounting images
- Timeline Analysis
- When was system installed, upgraded, booted, etc.
- Newly created files (malware)
- Changed files (trojans)
- Files in the wrong place (exfiltration)
- Digging deeper into Linux filesystems
- Disk editors
- Active@ Disk Editor
- Autopsy
- ExtX
- Basics
- Superblocks
- Directory entries
- Inodes
- Data blocks
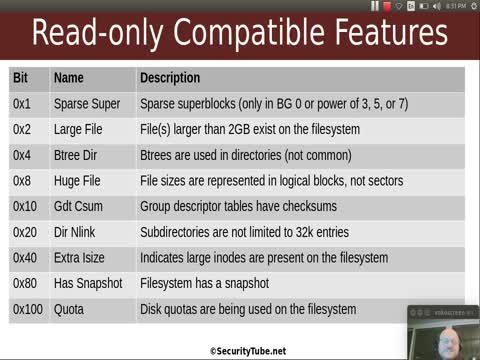
- Compatible, incompatible, and read-only compatible features
- Experimental features may be installed
- Boot code
- Using sigfind to find important blocks
- Understanding indirect block levels
- istat, ils, ifind, icat
- Links and mounts
- Hash trees
- Journaling
- jls
- jcat
- Finding data with blkstat, blkls, blkfind, blkid, and blkcalc
- Relating data found with grep to a file/application
- Finding block size, etc.
- Using grep with a keyword file
- Seeing data in context
- Associating a file with the data
- Undeleting files
- Searching unallocated space
- Basics
- Disk editors
- Network forensics
- Using snort on packet captures
- Using tcpstat
- Seperating conversations with tcpflow
- Tracing backdoors with tcpflow
- File forensics
- Using file signatures
- Searching through swap space
- Web browsing reconstruction
- Cookies
- Search history
- Browser caches
- Unknown files
- Comparing hashes to know values
- File command
- Strings command
- Viewing symbols with nm
- Reading ELF files
- objdump
- Bringing out big guns - gdb
- Memory Forensics
- Volatility Profiles
- Retrieving process information
- Recovering command line arguments
- Rebuilding environment variables
- Listing open files
- Retrieving bash information
- Reconstructing network artifacts
- Kernel information
- Volatile file system information
- Detecting user mode rootkits
- Detecting kernel rootkits
- Reversing Linux Malware
- Digging deeper into ELF
- Headers
- Sections
- Strings
- Symbol tables
- Program headers
- Program loading
- Dynamic linking
- Command line analysis tools
- strings
- strace
- ltrace
- Running malware (carefully)
- Virtual machine setup
- Capturing network traffic
- Leveraging gdb
- Digging deeper into ELF
- Writing the reports
- Autopsy
- Dradis
- OpenOffice
Linux Forensics Course Videos
Dr. Philip Polstra

Dr. Philip Polstra (Dr. Phil) has been involved with technology since an early age. He and one of his brothers cleaned out their savings to purchase a TI-99/4a computer in the early 80’s, much to the chagrin of his parents. He has been tinkering with computers and electronics ever since. Phil is an internationally recognized hardware hacker and information security expert. He has made repeat appearances at several of the top conferences worldwide. Here are just a few of the conferences he has spoken at: DEFCON (six times in four years), Blackhat, 44CON, GrrCON, BruCon, ForenSecure, SecTOR, c0c0n, Shakacon, B-sides Detroit, and B-sides Iowa. His work on developing small affordable hacking devices is documented in the book “Hacking and Penetration Testing with Low Power Devices”. He is also known for his work on USB hacking and forensics. Phil has published several articles on USB-related topics.
Phil is an Associate Professor in the department of Math, Computer Science, and Statistics at Bloomsburg University of Pennsylvania where he teaches Digital Forensics. His current research focus is on developing ultra-low-power hacking hardware. Phil also performs security penetration tests and forensic investigations on a consulting basis. His book “Linux Forensics” is considered a must have by a number of people in the forensics and information security community.
In addition to in-person training, consulting, presenting at conferences, and running conference workshops, Phil has also produced hundreds of instructional videos. His video courses are available at PentesterAcademy.com, PluralSight, O’Reilly, udemy.com, and elsewhere.
When not teaching, Phil enjoys spending time with his family, tinkering with electronics, attending infosec conferences, experimenting with software defined radio (SDR) and various aviation activities. Phil is an accomplished aviator with a dozen ratings, all of which are current. Phil’s ratings include Commercial Pilot, Flight Instructor, Airframe and Powerplant Mechanic, Aircraft Inspector, and Avionics Technician. His flight hours are measured in the thousands and he has been known to build aircraft.
Books Authored by Philip

Linux Forensics (5 Stars on Amazon.com)
Linux Forensics will guide you step by step through the process of investigating a computer running Linux. Everything you need to know from the moment you receive the call from someone who thinks they have been attacked until the final report is written is covered in this book. All of the tools discussed in this book are free and most are also open source.

Hacking and Penetration Testing with Low Power Devices (4.5 Stars on Amazon.com)
Hacking and Penetration Testing with Low Power Devices shows you how to perform penetration tests using small, low-powered devices that are easily hidden and may be battery-powered. It shows how to use an army of devices, costing less than you might spend on a laptop, from distances of a mile or more.
The book shows you how to use devices running a version of The Deck, a full-featured penetration testing and forensics Linux distribution, and can run for days or weeks on batteries due to their low power consumption. Author Philip Polstra shows how to use various configurations, including a device the size of a deck of cards that can easily be attached to the back of a computer.
 Linux Forensics
Linux Forensics